In April the Government released its 2023 Cyber Security Breaches Survey. The importance of the survey is to outline the current state of cybersecurity resilience amongst businesses, organisations and charities operating in the UK. The survey highlights the latest threats, reveals how organisations are responding, and explores the ‘policies, processes and approaches to cybersecurity’ by UK industry.
While at first glance the findings appear similar to previous years, there are some subtle changes in them that should spark concern amongst IT leaders and those in charge of protecting their organisation’s digital estates.
Worryingly, the survey found that cybersecurity could be falling down the list of items of most importance. The figures highlighted a 12% drop in companies placing online security as a top priority from 80% to 68% for smaller and micro businesses, with economic stresses and financial pressures understandably being blamed for the decline.
Further highlights also showed that the number of businesses implementing basic controls such as password policies, network firewalls, and restricted admin rights, had also all gone down by around 10% when compared to the previous year.
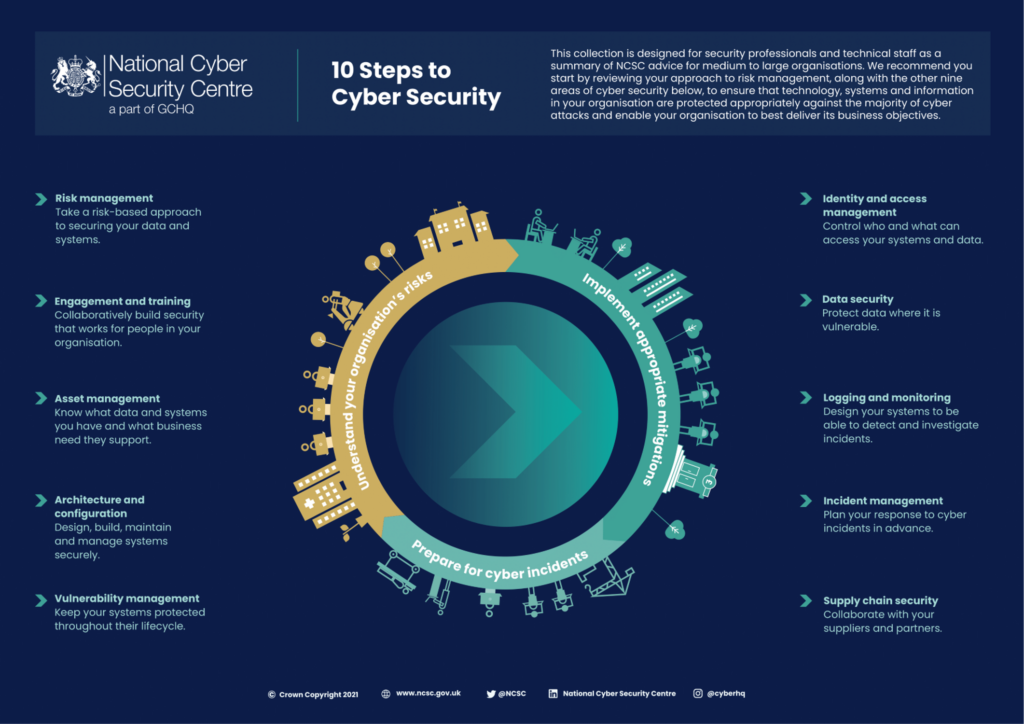
The Cyber Security Breaches survey also found that only 14% of businesses were aware of the Government’s cybersecurity ‘10 steps guidance plan’, and again only 14% were aware of the Cyber Essentials Scheme. So, while guidance on best protection and strategy is available, only a small proportion of businesses and organisations are actually accessing it.
These shifts may seem largely insignificant on the surface; however, they all indicate that smaller UK businesses are taking steps in the wrong direction to make sure that their digital estates are protected. This is all happening at a time when cyberattacks are making headlines on an almost weekly basis and cybercriminals are becoming ever more sophisticated in their approach. Last year more than half of SMEs had reported some form of cyber-attack, up from 39% the year before.
We understand that cybersecurity can be a daunting task for business owners and leaders, especially when time and resources are stretched. To help, we have broken down the Government’s ‘10 steps guidance plan’ into bitesize pointers to help organisations of all shapes and sizes improve their cybersecurity maturity.
The National Cyber Security Centre’s 10 steps to cybersecurity
- Risk management – This involves identifying what parts of your business have a digital presence and as such what the potential vulnerabilities are and what is at risk. Understanding this is the first step in building a robust cybersecurity strategy. You can analyse what needs to be online, and what doesn’t, and put the relevant security solutions in place to protect these processes.
- Engagement and training – Unfortunately human error still plays a prominent role in cybersecurity breaches and its why phishing attacks are still the most common attack vector being used by cyber criminals. Ensuring your staff are trained, not just to identify phishing attempts but all types of attacks, will help reduce the chances of a successful attack against your organisation. Training and investing in your staff are great ways to help build confidence amongst the workforce. Cybersecurity should be a collective effort across a company and not just left to the IT team to handle.
- Asset management – Like risk management, asset management is all about identifying risk. In short, it’s essential that you have an inventory of any computer, laptop or device that contains key company data and information, and is connected to the internet or internal network. If you know where your data is being stored and potential access points, you’ll know what you have to protect.
- Architecture and configuration – You should be constantly maintaining and improving your cybersecurity and IT systems and infrastructure. Providers of software and hardware understand that there may be vulnerabilities in their systems and should be providing patches and updates when these are identified. Make sure you stay connected with your providers, so you don’t miss out on these essential upgrades.
- Logging and monitoring – It’s impossible to know if you’re under attack if you’re not looking. Build cybersecurity systems which detect and investigate potential incidents so that you can adopt a proactive approach.
- Vulnerability management – This is the process of testing, analysing and identifying vulnerabilities in your IT infrastructure. You need to continually work to keep systems secure throughout their lifecycle. Regular testing can help to identify new and evolving vulnerabilities within your systems.
- Identity and access management – Keep a log of everyone that has access to company hardware and important data and information. You can also control what permissions each of your users have. When setting up access management ask yourself, what does this employee really need to do their job effectively, and then set their permissions from there. By better regulation and restriction of parts of the environment, you can quickly reduce the level of potential risk.
- Data security – Work to understand where your data is vulnerable and introduce solutions and processes to protect it.
- Incident management – Every organisation should have a robust plan in place should they suspect they are under attack. In the event of an attack, every employee should be aware of their role in helping to reduce the damage, who to contact and the next steps for getting your organisation back up and running with minimum disruption. Incident Response plans are also a critical part of most cybersecurity insurance policies, so don’t be surprised if your provider asks you about yours.
- Supply chain security – Cybercriminals are now using third parties as access points to breach other organisations. You should work closely with your suppliers and partners to understand their security postures, in order to ensure their vulnerabilities do not pose a threat to your organisation.
For more information on The National Cyber Security Centre’s 10 steps to Cyber Security visit here. Or to learn more on how BOM IT Solutions can help, visit our specific cyber security website pages, contact a member of our team at 0800 038 7222 or sales@bom.co.uk
Credit: National Cyber Security Centre